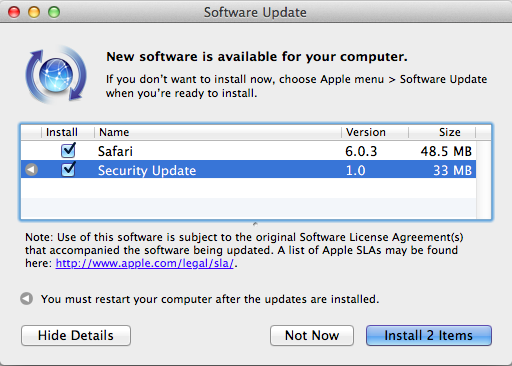
Windows PC and Android users are used to the continuous stream of updates available for both operating system and applications software. Even iOS users receive a regular diet of app updates. The flow of updates for Apple software is relatively scant by comparison. That changed this week with Apple releasing updates for all of their major software platforms, including iOS, MacOS, their Safari browser, WatchOS, tvOS and both iCloud and iTunes on Windows platforms.
What prompted so many updates all at once? Security.
Aren’t Apple devices secure? Well, yes, and no.
We are used to hearing that Apple operating systems and software products are pretty secure (although no product can ever be assumed to be 100% secure), Apple product have a well-deserved reputation for being safer than Windows products. That belief was shaken this week, even if it has previously been wobbled with a fairly steady stream of Mac OS X and even iOS malware variants being discovered by security vendors. That said, the core operating systems have remained quite ‘security hole free’. Patches for security issues have been release before by Apple, but the sheer number and scope this recent flurry of patches is quite unprecedented in the Apple software ecosystem.
What type of security problem causes so many patch from the Apple corporation in such a short time?
The security problem Apple patches was a critical vulnerability – a problem of the worst type – a hole that allowed a remote user to run privileged code on the target device, without need for end-user intervention, clicks to approve or other interaction with the code, save receiving it in a text message.
This particular bug in iOS, meant that a carefully crafted text message, bearing a payload of malicious code, could run code at will, and without detection. This really was the worst type of operating system bug, and to make matters worse, the faulty libraries were re-used in many different Apple products.
How could this bug affect my iOS device?
The way this bug is exploited is so simple, that anyone with some coding knowledge and your phone number could exploit your phone. The do not need physical access, and they do not need your password or PIN code. All they need to do, is send you an iMessage, or multi-media SMS message – or MMS message with the exploit code embedded inside a particular type of image file.
That image file must be an attachment of type ‘TIFF’ – which stands for Tagged Image File Format. Once received, your iOS device will run the code hidden inside the image file and give access to the phone operating system. With such access, the cybercriminal would be able to steal your contacts, your password or just about anything else from your iPhone.

More alarming is that an attack crafted and launched in this way would probably not be detectable and would require no user help what-so-ever to complete the theft of personal data, both immediately, and probably in an ongoing manner.
To look to a similar hole in the non-Apple world, we have to compare this bug to the rather terrifying Android bug named ‘Stagefright’ – which allowed malicious cybercriminals to access millions of Android phones and tablets, again using a carefully crafted MMS message.
Just how widespread could a malicious attack on Apple devices be?
Apple estimates that they have about a billion users between iOS and MacOS – and considering that all version of their code before this latest patch are all vulnerable, I estimate the number of potentially affected devices at many, many, many millions.
Who do we thank for the fix?
We actually have to thank one Tyler Bohan, a senior security researcher at Cisco Talos – a division of Cisco which researches security and provides reports and intelligence on said security matters.
Such an attack would be quite serious in an iPhone or iPad, but it could be even more severe on MacOS computers. Unlike iOS, which has sandboxing technologies which prevent a malicious MMS from executing code without root access via a jailbreak, MacOS is much more open, offering the potential for an attacker to take full control of your machine.
We do know that patching your device to the latest version WILL prevent this particular exploit, so it is the preferred method of keeping you safe – so stop reading this article and go and apply the patches NOW!
Read more about Apple updates here: Apple Security Updates.

With all of the recent security updates, I now must enter my password for Outlook on each device whenever I try to access my email or anything else that is attached via email. While I still use hotmail, I never had this problem before, that is until after the recent Apple updates took place. How can I end this constant annoyance?