I just got an email from my bank – Wells Fargo – that says “Wells Fargo Bank technical department is performing alert upgrade to improve the security of our online banking notifications as part of our enhanced security measures”. Not suspicious, except the next line says “This is mandatory validation exercise for all Wells Fargo Bank customers. During the database upgrading exercise we discovered a credit advice of a substantial inflow in your favor.” What? Is this legit? I clicked on the link and it sure looks like Wells Fargo, but I’m scared to proceed in case it’s some criminal phishing hack or other.
You’re right to be suspicious and skeptical. What you’ve received is indeed a phishing scam and is not a legitimate email warning from Wells Fargo. If nothing else, Wells has writers with a much better sense of grammar. Go read those sentences again, you’ll see what I mean. Still, grammar isn’t the first red flag I saw in this email, but rather the obvious enticement of “we upgraded our database and found you had extra money”.
Does anyone fall for that sort of thing? And if this were from a bank, would they email you this information rather than send you a letter of explanation?
Unfortunately, people do fall for this sort of thing, skim messages, and don’t really pay close attention to either the wording or the URL on the link itself.
Let’s have a look at this phishing scam…
First off, here’s the email I received. I imagine yours was very similar:
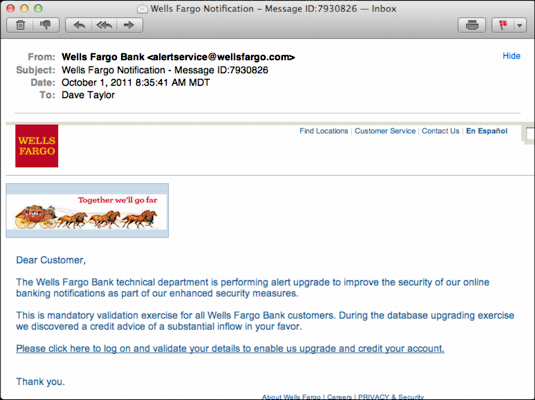
Not really legit, but it certainly looks realistic and even the sender address looks correct, “alertservice@wellsfargo.com”. But my email program does something that yours might do too: leave your cursor on an embedded link and it’ll show you the destination URL:
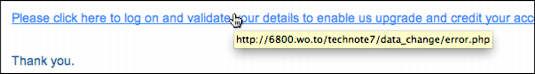
“wo.to”? The “.to” domain is the island of Tonga. Really. So why the heck would Wells Fargo be using an offshore server? The answer is obvious. They aren’t.
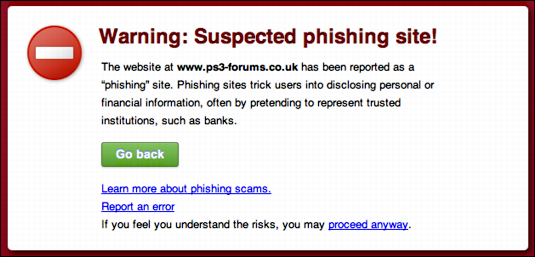
Still, what happens if you click on the domain? If you’re lucky, your Web browser has some anti-phishing filter already installed and pops up a warning:
But maybe it doesn’t — or you’re skeptical or lured by the promise of additional money dropped into your account — and you end up on the site itself:

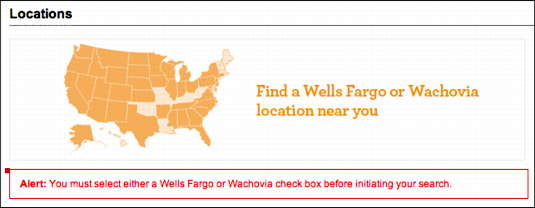
This looks totally legitimate and valid, doesn’t it? Very impressive. In fact, if you enter a zip code to find an ATM, it’ll even take you to the proper page on the Wells site itself:
Back on the fake site, though, if you were to log in using your proper credentials, which is of course the entire point of this sort of phishing message in the first place, you’d even be taken to a legit Wells Fargo page:

No surprise, though, it still says “Sign On” because you didn’t actually sign in to the real site in the first place, you just gave your login credentials to the criminals who will quickly log into your real site, change your password, then drain all the money into one of their own accounts.
That’s how these work. Your best rule of thumb for avoiding phishing attacks? Be incredibly skeptical and never click on any links included in email messages. That’s it. If you think this might be a real message from Wells Fargo, for example, simply type in “wellsfargo.com” into your Web browser and see whether there’s a real message from the bank or not.
And be careful out there…

I clicked on almost all of the click ons at the end of the email and could not click on “About Wells Fargo” and, also could not click on “PRIVACY & Security”. Imagaine that.
But these guys are good. Almost ricked me.