A friend of mine sent me a URL for a Web site that ended in .onion. Chrome can’t handle it and says it’s bogus, but he insists it’s legit. How do I get to the site referenced?
Given the nature of the .onion world, I suspect that the site he shared with you is not one that you’d ordinarily encounter on the regular web: it’s a site referencing system used on the so-called “Dark Web”. The problem with the regular web that it addresses is that ICANN, the organization that supervises all domain name – including askdavetaylor.com – can at any time decide it’s a violation of their terms and cancel it. Doesn’t happen with big sites but if you’re already skirting the law you don’t want a third party suddenly yanking out the rug from under you.
Enter .onion domains. With no registrar, these domain names are actually a portion of a public key encryption of the address of the site. Use a Web browser that knows how to expand one of these domains and it can figure out how to connect. Here’s a slightly more detailed explanation:
“.onion” sites are the first half of the base-32 encoded SHA-1 hash of a public key from a 1024-bit RSA key pair, with the suffix “.onion” appended. A .onion domain name will always be 16 characters long and will only contain lowercase letters a to z and the digits 2 through 7.
So how do you use it? You need something called a Tor browser, an open source Web browser that’s designed specifically for people who are seeking to explore the deep web and even the regular web, but with much more anonymity. You can grab a Tor browser for free and try it, all from torproject.org.
Don’t freak out, though, because the Tor browser and network came from the US military, an early Defense Advanced Research Projects Agency (DARPA) project that was transferred to the Electronic Frontier Foundation (EFF), who spun out the Tor Project as a way to further development of the software system.
It’s complicated, there’s no way around it, but the good news is that once you have Tor Browser installed on your computer, it’s just another address to copy/paste and visit. Let’s have a look!
First off, here’s the reference Web site address we’re going to try and visit: uj3wazyk5u4hnvtk.onion
Try to visit it with a traditional browser like Google Chrome and you’ll get this sort of error message:

You can reload as many times as you want, but the fact is that Chrome doesn’t know how to interpret and decode .onion domain names. Instead, grab that Tor browser and launch it. You’ll see this:

As explained on the page, Tor isn’t just for dark web and illegal activity, there are plenty of places you might want to visit online that are safer for you with certain level of privacy and anonymity. Definitely explore Tor once you’ve launched it.
But let’s get back to our .onion Web address, because now you’re in a browser that can interpret it. A click and here’s where you end up:
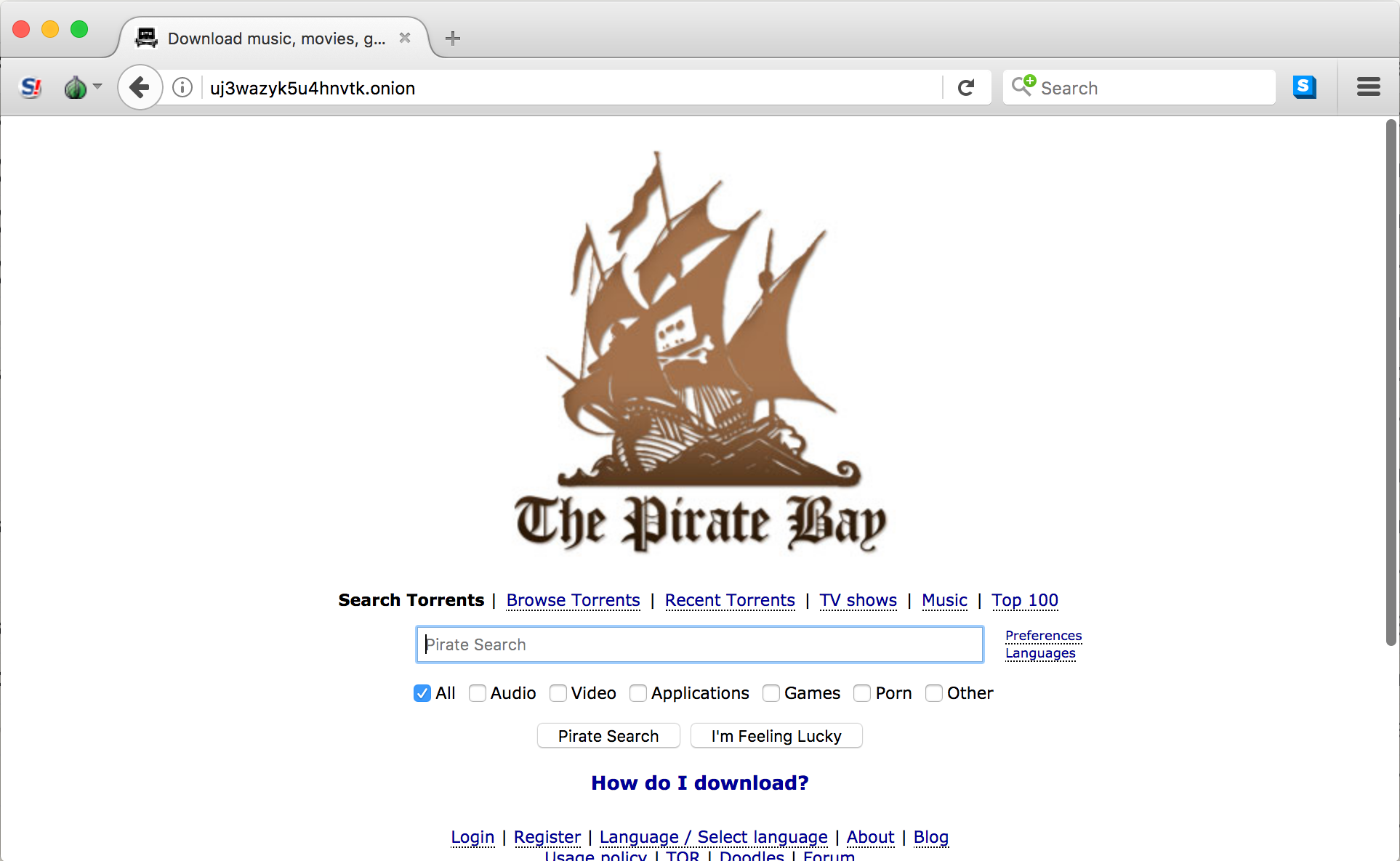
Notice what’s shown in the address bar above. It worked!
What makes Tor Browser so interesting is that it automatically uses the onion network to bounce all your queries from proxy server to proxy server, as shown:
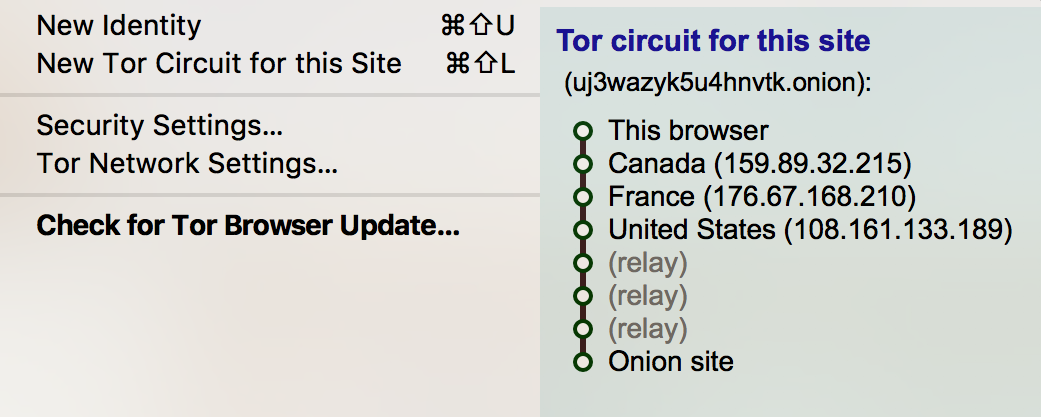
Notice that my computer bounces to Canada, France, back to the United States, through three relays, and then finally onto the Onion site (The Pirate Bay). Slick, isn’t it? Not only that, but click on “New Tor Circuit for this Site” and it’ll find a new route without interrupting your site visit.
And now you know. Turns out .onion domains are quite interesting!

Is it possible to track someone who is using the Tor browser by following the relays back to the source?