So confused. I went to a Web site and suddenly an Adobe Flash Player update popped up, telling me it was required to view content on their site. But I looked at the page and there’s no Flash content. Is the update page legit or a bogus scam?
I’m so impressed that you’re skeptical about these sort of things because if your Flash player needs an update, it’s the player itself that will pop up the update window, meaning it won’t be part of the Web page that has the content in question. Instead, I believe you’ve bumped into one of the newer forms of malware distribution, a very smart design that is predicated on us users blindly clicking “update” if we’re told something we’re running is out of date.
How can you tell? As always, pay attention to the URL. Where’s the message coming from? Where is it taking you after you click — though you should never click if there’s even the slightest doubt.
Let’s look at one I bumped into while reading an article on Slate.com, a quite reputable Web site:
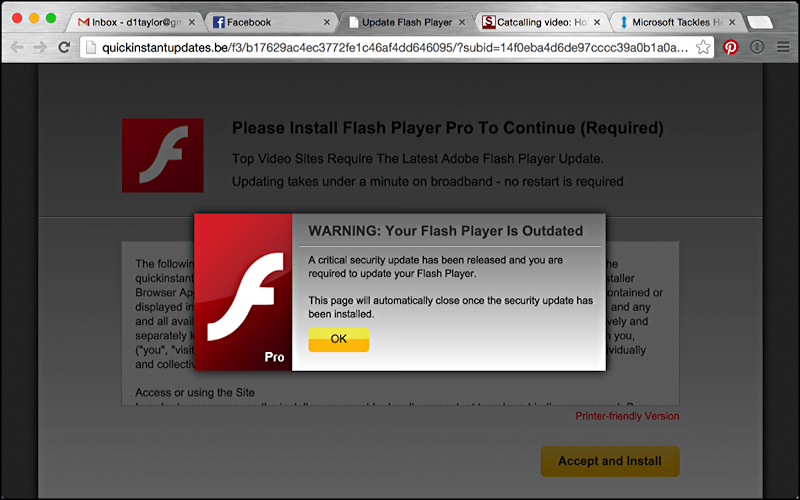
Looks legitimate, though there are a few things that made me instantly suspicious. First off, the pop-up window is part of the landing page, not coming out of the Flash player itself. There’s also some odd wording, like “Top Video Sites Require The Latest…” rather than something more like “This site has content that requires…”
Still, it’s the URL that was a big red flag. Look more closely at it:
![]()
“quickinstantupdates.be”. That’s really odd. The “.be” domain is Belgium, but more importantly, it’s not adobe.com or similar, so that’s a major problem.
To confirm, look what you see when you go to that URL without all the odd stuff appended:

That’s definitely more than just a bit suspicious.
To learn more, I used the online whois service to look up the information associated with this particular domain and, well, it’s the capper:
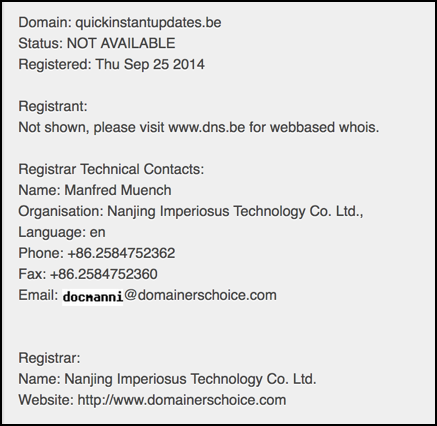
Manfred might be a lovely person, but there’s no reason in the world why an Adobe Flash update would be served up by a Belgian Web site owned by someone in China.
It’s a scam. It’s a way for them to infect your computer. And it’s smart of you to be skeptical and avoid the trouble!
Remember, be careful out there.

THANKS FOR THE INFO. I THOUGHT SOMETHING LIKE THIS WAS GOING ON. I HAVEN’T BEEN ABLE TO STREAM SPORTS FOR A WEEK IN CENTRAL CALIFORNIA AND WONDERED IF I WAS BEING STUPID. A LOT OF INTERNET SOLUTIONS INVOLVE WAY MORE COMPUTER SKILLS THAN I WANT TO DEAL WITH. 23APR15. IT SURE SEEMED LIKE A HACK JOB. NEEDS TO BE A CAPITAL CRIME ALONG WITH IDENTITY THEFT.
Same error happened to me visiting LinkedIn via the Chrome browser on a PC.
I just went through this “Adobe Update” scam. I was on the verge of executing the file but it did not look right. There were moving arrows directing me to activate the download on the “download bar”. I’ve never seen that before. Checking the URL I discovered this window was from “quick computer repairs”. (http://quick-computer-repairs.be/f3/1cea36ca8c2b6384cba4ba5dfeddfcb0/?subid=7c02009edf676661c91c42bf3f3a83d3&transaction_id=c34d784d-1f0b-4326-af46-f16beb9c6a7e&rand=5456267485363&source=mbs-f3)
Those downloads were quickly deleted.
Checking on the Adobe site my player was up to date. You can’t let your guard down…
This came up for me too, also on Slate (on Chrome, no adblock or anything in place), and I did not click on anything like a link that would have brought it up. It’s the kind of virus spam that pops up on pirated sports tv sites–why would it be on Slate? Have they been hacked? Or are they not screening their advertisers properly?
Justin, yeah, I think they’ve been hacked. In fact, I was reading about a widespread Drupal hack that has affected millions of sites and am wondering if Slate is one of them. Stinks.
Would there be any way to trace the source of the malvertising? I’ve experienced the exact same redirect from my own website to multiple different spammy domains listed below:
quick-computer-repairs.be
quickinstantupdates.be
fastpcupdatenot.be
fast-update-apps.be
simpleinstant-update.be
All want me to install some bogus Flash, but it only happens when I preview a post.
Are you running Drupal? There’s a widely disseminated exploit in the Drupal code base…
Unfortunately not, I’m running the latest version of WordPress.
However I spent a few hours going through my approved Adsense ads (I’ve always let Google approve/disapprove them automatically for me) and found two other similar ads that immediately hijacked the browser and sent it to a spammy dating site. I was a little bummed not to find the Flash redirect, but it’s making me think Adsense may be the source. I wonder if Slate is running Adsense as well.
I’ve been seeing the same thing on Slate.com for weeks. Normally I’d just close the window and move on, but it’s straight up closing the window I have Slate open in, so it’s preventing me from reading articles. Also, how is it able to hijack Slate’s presence? Is it targeting Slate, or is it targeting my machine? If it’s targeting me, is there a way to get rid of it?
What do you suggest to do if someone might have clicked on the update and let it install something on your Mac?
Probably you’re okay, most of these are targeted at PC users, not Mac users.
I had the problem, and by paying Apple tech’s $19.00, it took them 4 1/2 hours to get the Adobe Flash Player to work as, previously on my desk top Mac computer, I could not get it to work. Is “Download For Mac” necessary or worthwhile?
Bill
4 1/2 hours to get Flash working? I’d say that unless you’re visiting sites I don’t know about, it wasn’t worth the effort. The entire Web is migrating to HTML5 and leaving Flash in the dust. And – more importantly – pay attention to this article, Bill, as it’s about a malware scam that installs evil software on your system, not about a legit Adobe Flash Player update in the first place.
THNAKS FOR THIS I HAD SAME PROBLEM ALSO