It’s an unfortunate fact that web security sometimes gets lost in the excitement of setting up a new website or blog, the thought of finally having a storefront for your craft takes precedence over protection from SQL injections and Distributed Denial of Service (DDoS) attacks – as if anybody knows what they are anyway. Foregoing website, server, and/or database protection creates a false economy though; online threats are increasingly a concern for everybody who has a website.
The Dark Web – While it’s easy to dismiss cybercrime as the pastime of society’s outliers, the growing popularity of for-hire hacking has created a strange perversion of e-commerce on the internet’s underside, the mysterious dark web. Hiring a “botnet” (a term that describes a group of hijacked devices pooled together for nefarious means) of 1,000 devices costs about $7 an hour – with loyalty points awarded for purchasing on some sites.
It’s not the customer-first world it might appear to be though. For example, let’s say that somebody wanted to launch a DDoS attack on Sony’s website, and stumped up the money to the modern equivalent of a man in a dark alley; there’s no regulation to stop the trader taking your payment and running off with your card details too. To paraphrase an article from Quartz about identity theft on the dark web, it’s impossible to verify who or what is real on the internet’s underside.
For all the treachery inherent in cybercrime though, DDoS attacks and SQL injections do happen. The latter, a way of inserting code into a database so that it does something it’s not supposed to, accounted for 51% of all attacks on web applications. Popular blogging site WordPress had to patch out a vulnerability that could permit SQL injections on its users as recently as the end of January.
SQL Injections – The uncomfortable truth is that the availability of web application firewalls or “WAFs” should have consigned attacks like SQL injections to the same box as AOL installer CDs and Geocities sites – the technique is more than a decade old. WAFs are designed as an all-in-one solution to internet malcontents, keeping the bad guys away from your site and protecting against many threats such as cross-site scripting (a common threat on WordPress) as well as remote file inclusion and illegal resource access.
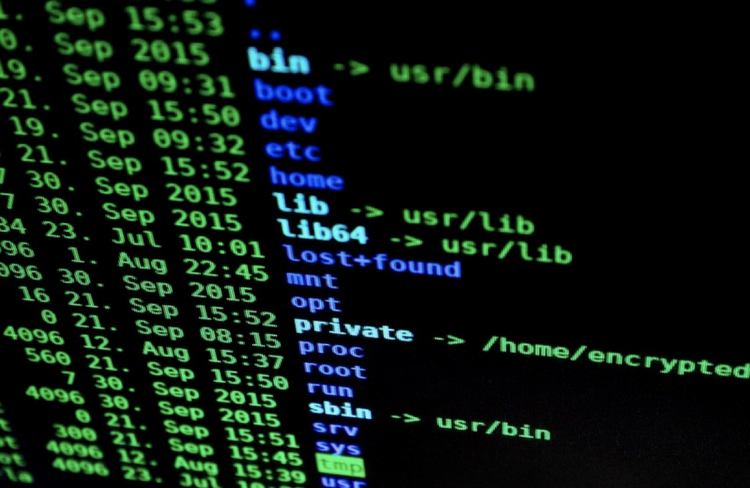
Existing in the cloud (they don’t require the installation of hardware or software on a client computer), WAFs act as a filter or barrier between sensitive systems and the internet. A firewall provider can also help small businesses comply with PCI DSS, a type of data security standard that aims to reduce credit card fraud; in fact, a firewall is point one on the checklist.
Despite the increasing accessibility of WAFs and the ease defence against SQL injections, the technique remains the number one threat to websites according to the Open Web Application Security Project – why? The answer lies jointly with developers and hackers. In the latter case, it’s the ease at which SQL injections can be deployed but corporate culture has its part to play in preserving an old nuisance too.
Bonuses tied to deadlines, a lack of regulation around business security, and a widespread inability for IT folk to communicate the importance of staying safe online to laypeople are the reasons simple threats like SQL injections continue to cause chaos. It might be easy to install a WAF as a failsafe but basic threats will continue to exist as long as upper management presents a willingness to let them in.
Do the work, make sure you have all the necessary hardware, software and settings, and be safe out there!
This is part of a series of security and online safety articles here on AskDaveTaylor. Have a related topic you’d like us to discuss? Please let us know. Image credit Pixabay.

I’m having the same problem. Can someone help me? Thanks!