It sounds like one of those rumors that seem to be created by anti-virus software companies to sell their software, a terrifying warning that in 48 hours all of your programs will stop working and your address book will be sent to some shadowy organization in Eastern Europe to analyze, but in fact the DNSChanger malware is a legitimate problem and is known — through dissecting and analyzing the code — to be poised to effectively disable your ability to look up any domain names starting on Monday, July 9, 2012.
Without the ability to look up domains using the Domain Name System (DNS) your computer will indeed be effectively cut off from the Internet, and restarting or unplugging and re-plugging in your modem won’t solve a thing.
Not good.
Here’s how you can test to see if you’ve been infected by DNSChanger, and if so, what you can do to remedy the situation…
In case you are still skeptical, turns out that the Federal Bureau of Investigation (FBI) has issued a general warning about this, part of what it sees as the growing threat of cyberattacks: DNS Malware: Is Your Computer Infected? In that article, they explain that it’s not that the malware is going to start working on July 9, but that the temporary system they set up so that if it is running on your computer you can still get to the Internet is going to be shut down on July 9:
“Update on March 12, 2012: To assist victims affected by the DNSChanger malicious software, the FBI obtained a court order authorizing the Internet Systems Consortium (ISC) to deploy and maintain temporary clean DNS servers. This solution is temporary, providing additional time for victims to clean affected computers and restore their normal DNS settings. The clean DNS servers will be turned off on July 9, 2012, and computers still impacted by DNSChanger may lose Internet connectivity at that time.”
If you have been infected, this means that the FBI has let you ignore the problem, possibly for months. But as of the next few days, their hidden solution will stop solving and you’ll be in a right pickle.
So let’s have a look at an easy way you can test to see if you’re infected.
If you know how to get to your own DNS information on your computer (Mac users, this is easily done via System Preferences, as I detail here: Find your DNS servers on a Mac, while Windows users can get the same info by clicking “Run…” from the Start menu and type “ipconfig /all”).
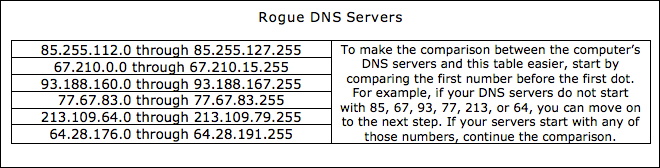
Compare what you have with this table of rogue DNS servers from the FBI:
Fortunately, you don’t have to be a geek to test things. Instead, simply go to http://www.dns-ok.us/ and it’ll hopefully pop up this message:
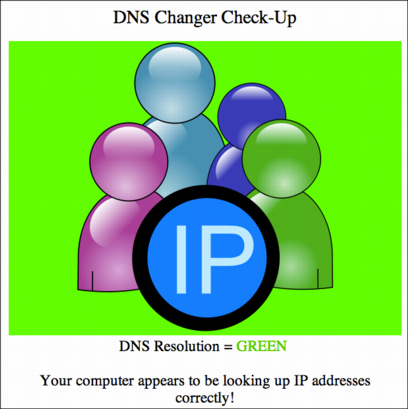
*phew*
If you are infected, here’s what you’ll see instead:
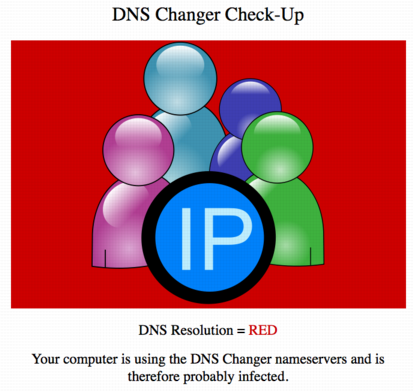
Don’t panic. You know that there’s a problem and there are a number of companies that are offering their anti-virus or anti-malware utilities for free. Here are few to consider:
Pick your favorite, run it, let it try and fix the problem, then check the result against http://www.dns-ok.us/ until you get things working.
Tip: Always have good backups of your files. If you’ve been infected by DNSChanger, you might well have other malware on your computer too. Be safe, be paranoid and be redundant for anything that it would be painful to lose.
I hope that everyone tests their system to confirm it’s clear and, if you do have a problem, fix it before that July 9 deadline rolls around and you’re offline. Good luck.

Sir i have a question. what if i got infected by the DNS changer malware/virus and i use the system restore will the malware/virus remain in my system/hardware? thank you in advance =3
Apparently they are rather drowning in users testing their computers. I’d try tomorrow morning but if you can still get online tomorrow, you’re probably good to go anyway, MaryKay.
Hey Dave,
Thanks – the link is coming up Server Not Found. Perhaps they are over run?
“) MaryKay
In Mac and Linux, as you know, it is not possible to change DNS address without root / sudo access.
As such I suspect it would be a Windows only issue.
Hopefully you tested negative, Whitney? I’d appreciate hearing from someone who tests positive, btw. Just use that handy contact form…
Wow, I had no idea. Thanks for the info!